Hardware Root of Trust: When Is It Necessary
author
In renewable energy and connected infrastructure, a hardware root of trust becomes necessary when compromised devices can disrupt smart grids, energy monitoring, or building automation at scale. For buyers and engineers navigating the IoT supply chain, verified IoT manufacturers, Matter protocol data, and smart home hardware testing are essential to separate marketing claims from measurable security, compliance, and long-term operational resilience.
When does hardware root of trust become non-negotiable in renewable energy systems?
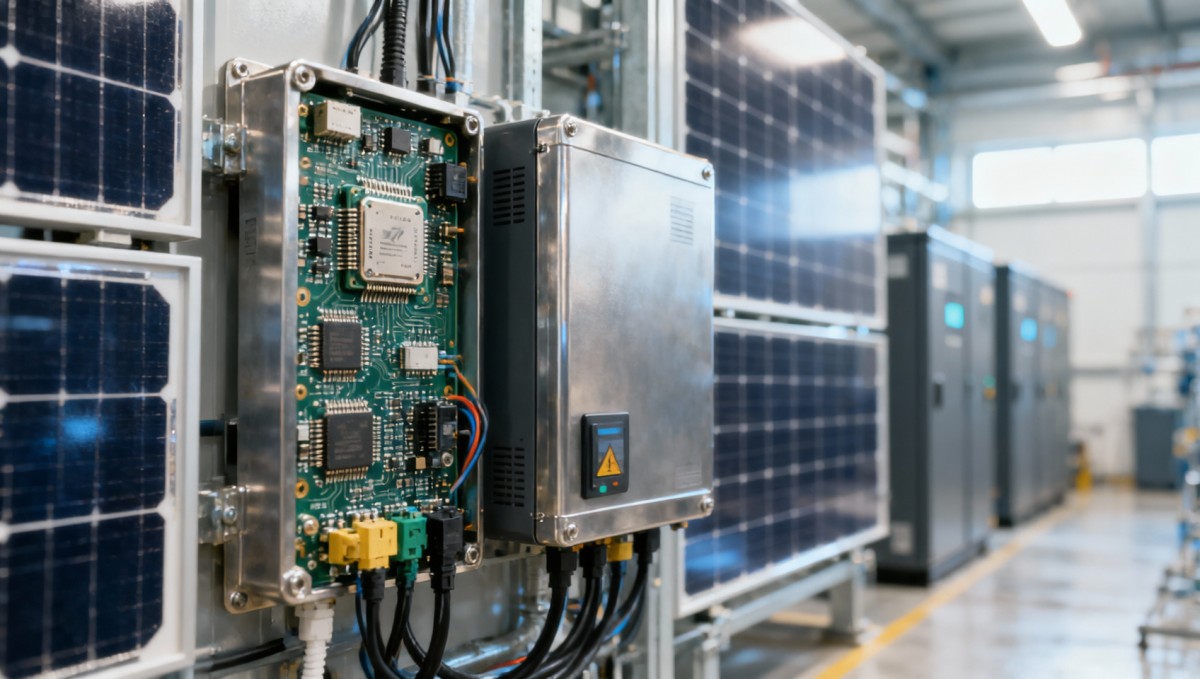
A hardware root of trust is not a decorative security feature. It is the device-level foundation that anchors identity, secure boot, key storage, firmware integrity, and trusted updates. In renewable energy environments, this matters because inverters, gateway controllers, battery systems, smart relays, and edge monitoring nodes do more than collect data. They influence load balancing, dispatch timing, access control, and operational continuity across distributed assets.
The answer to when it is necessary is practical rather than theoretical. If a device can change setpoints, open or close power pathways, modify telemetry, or become an entry point into a broader energy network, a hardware root of trust should move from optional to required. This threshold is often reached in solar-plus-storage projects, microgrids, EV charging coordination, smart commercial buildings, and remote energy monitoring deployments operating across 24/7 cycles.
For information researchers and business evaluators, the core issue is risk concentration. A single compromised low-cost node may look insignificant in a pilot with 10 devices, but the exposure changes in fleets of 500, 5,000, or multi-site deployments spanning 3 regions. Protocol fragmentation compounds that risk. A device claiming compatibility with Matter, Zigbee, BLE, or Thread does not automatically prove secure identity management, secure provisioning, or tamper-resistant key handling.
This is where NexusHome Intelligence aligns with the needs of renewable energy buyers. NHI’s value is not in repeating vendor claims but in translating hardware trust into measurable verification across connectivity, smart security, energy control, PCB-level component quality, and real-world stress behavior. In an industry where packet loss, latency spikes, or unstable power conditions can have operational consequences within seconds to minutes, engineering truth matters more than branding language.
Typical situations where hardware trust should be mandatory
- Grid-interactive assets that receive remote commands, such as battery energy storage controllers, smart breakers, and PV inverter gateways.
- Building energy systems that link HVAC automation, occupancy sensors, access control, and demand-response logic in one integrated platform.
- Remote installations where truck-roll costs are high and secure over-the-air updates must remain reliable over 2–5 year maintenance windows.
- Multi-protocol environments where Matter, Thread, Zigbee, Wi-Fi, or BLE nodes share control paths or sensitive energy data.
The procurement implication is straightforward. If the cost of device compromise exceeds the premium of secure hardware, then a hardware root of trust is necessary. In renewable energy, that premium is often far lower than the downstream cost of downtime, incident response, site visits, warranty disputes, or failed compliance reviews.
Which renewable energy applications need it most?
Not every connected device requires the same security architecture. A passive environmental sensor with no control authority has a different risk profile from an edge gateway that aggregates meter data, manages certificates, and pushes firmware to field devices. Buyers often overspend on low-risk nodes and underspecify high-impact ones. A scenario-based approach improves both security and budget discipline.
In renewable energy and smart infrastructure, the highest-priority use cases usually involve three factors: command capability, network bridging, and long service life. If a device is expected to operate outdoors, withstand thermal variation, and remain active for 3–7 years while handling cryptographic material, trust cannot rely only on software. Hardware-backed identity and secure boot become operational controls, not just IT controls.
The table below helps distinguish where a hardware root of trust is generally essential, conditionally recommended, or lower priority. This view is useful for procurement teams comparing BOM impact against operational risk in solar, storage, and building energy projects.
The key reading is that necessity rises sharply when the device sits at a trust boundary. Gateways, control hubs, and devices that bridge protocols deserve the most scrutiny. In renewable energy portfolios, these are often the same nodes expected to support remote updates, certificate rotation, and multi-tenant access over long operating periods.
How operators and buyers should classify field devices
A useful working method is to group devices into 3 tiers. Tier 1 includes command-capable or network-bridging hardware. Tier 2 includes measurement devices whose data influences billing, energy optimization, or compliance reporting. Tier 3 includes low-impact endpoints with limited system reach. In most projects, Tier 1 should require hardware-backed trust by default, Tier 2 should be reviewed against data criticality, and Tier 3 can be assessed more selectively.
This tiering also helps control cost. Instead of forcing the same security bill of materials across every node, teams can focus on the 20% of devices that create 80% of systemic risk. That approach is particularly useful in price-sensitive OEM or ODM sourcing where secure hardware components, provisioning processes, and firmware signing infrastructure affect lead time and unit economics.
NHI’s benchmarking perspective is valuable here because renewable energy procurement is rarely only about a single chip or module. It is about the interaction between protocol compliance, latency under interference, battery behavior, local processing speed, and long-term drift. A secure element on paper does not compensate for unstable PCBA quality or unreliable field update behavior.
What should procurement teams evaluate before approving a device?
Many sourcing errors happen because teams ask whether a device has security, instead of asking how that security is implemented, validated, and maintained. In renewable energy deployments, procurement should verify at least 5 core areas: secure boot, hardware-protected key storage, device identity provisioning, signed firmware update support, and field recovery controls. Without those checkpoints, the phrase hardware root of trust can be reduced to vague marketing.
Delivery reality also matters. A secure architecture that depends on complex custom provisioning may extend qualification by 2–4 weeks, while another design may support smoother factory onboarding and deployment at scale. Procurement teams therefore need a checklist that balances security depth with operational fit, manufacturer maturity, and integration burden across protocols such as Matter, Thread, Zigbee, or Wi-Fi.
The following table summarizes practical evaluation criteria for information researchers, operators, purchasing staff, and commercial reviewers comparing connected energy hardware suppliers.
This framework helps avoid a common mistake: approving devices based only on feature lists. For energy and building automation buyers, the better question is whether the supplier can prove secure and stable behavior through repeatable tests, engineering documentation, and realistic deployment conditions.
A 4-step procurement decision model
- Define the device role: read-only, control-capable, or protocol-bridging. This determines security depth and budget priority.
- Verify the trust chain: boot integrity, identity lifecycle, key handling, and signed update path should be documented.
- Review deployment fit: consider temperature range, power profile, communications stack, and expected service life of 3–7 years.
- Stress the real scenario: ask for evidence from interference testing, multi-node behavior, and remote recovery workflows.
For procurement teams under delivery pressure, this model also shortens internal alignment. Engineering can focus on technical trust anchors, operations can review maintainability, and commercial teams can assess total risk exposure instead of initial unit cost alone.
How does hardware root of trust compare with software-only security or lighter alternatives?
A frequent question is whether software controls alone are enough. In low-risk consumer devices, they may be acceptable. In renewable energy infrastructure, that answer changes when devices are remotely managed, physically accessible, or expected to maintain trust over years of updates. Software-only security can protect communications and application logic, but it is weaker when the device identity, firmware verification, or key material can be extracted or altered more easily.
That does not mean every project needs the most expensive security architecture. The better comparison is between acceptable risk and system consequence. If a failed endpoint only causes temporary local data loss, lighter measures may be sufficient. If compromise can spread across a smart building, distort energy settlement, or interrupt automated demand response, the economics favor hardware-backed trust even with higher BOM and integration effort.
The practical trade-off usually appears in three areas: component cost, manufacturing complexity, and deployment workflow. Secure elements, trusted execution environments, or microcontrollers with embedded security features can add sourcing and provisioning steps. However, those costs are often predictable, whereas breach recovery, asset replacement, and reputational damage are highly variable and frequently much larger.
Comparison logic for budget-constrained projects
- Use software-first protection for short-life, low-impact, non-bridging devices with narrow permissions.
- Use hardware root of trust for gateways, controllers, credential-bearing devices, and assets exposed to remote updates or harsh field conditions.
- Consider hybrid strategies when fleets contain both critical and low-criticality nodes, especially in mixed solar, storage, and building automation networks.
Where NHI’s testing approach adds decision value
This is exactly the point where buyers need independent engineering filters. NHI examines whether security claims survive real protocol loads, local processing demands, interference, standby power limits, and PCB-level reliability expectations. In renewable energy, trust is not only cryptographic. It is also whether the device maintains stable operation under thermal stress, congested wireless conditions, and long unattended service intervals.
That matters for business evaluators because price-only sourcing often hides lifecycle costs. A cheaper module that fails secure onboarding, drains backup batteries faster than planned, or behaves poorly under Matter-over-Thread congestion can delay commissioning and increase field support overhead over 12–36 months.
What compliance, implementation, and operational checks should teams plan for?
Security architecture only works when matched by process discipline. For renewable energy projects, implementation planning should cover factory provisioning, credential handling, field commissioning, firmware governance, and retirement procedures. Teams often focus on initial onboarding but neglect the later stages of certificate renewal, key revocation, or controlled decommissioning. Those stages become critical in multi-site deployments after 12, 24, or 36 months.
Compliance expectations also vary by region and application, but buyers should still look for alignment with broadly recognized practices: secure development lifecycle, controlled update signing, auditable access, privacy-aware local processing where applicable, and role-based operational control. In smart buildings and distributed energy systems, these checks matter because energy data may intersect with occupancy, access, or operational behavior.
A practical rollout often works best as a 3-stage process. Stage 1 covers lab validation and protocol benchmarking. Stage 2 covers pilot deployment in one site or one subsystem for 2–8 weeks. Stage 3 covers scaled rollout with monitoring for update success rate, latency behavior, battery degradation, and incident response readiness. This sequence reduces the chance that a secure-looking design fails under real operating conditions.
Common mistakes that increase project risk
- Treating protocol compatibility claims as proof of secure implementation, especially in Matter and multi-protocol environments.
- Ignoring component-level quality, even though unstable sensors, weak batteries, or poor PCBA execution can undermine security operations.
- Underestimating field recovery planning, which becomes costly when remote assets fail after an interrupted update.
- Evaluating only unit price instead of lifecycle cost across service visits, downtime, and delayed commissioning.
FAQ: questions buyers and operators ask most often
Below are recurring questions from research teams, operators, and procurement managers comparing connected energy hardware.
Is hardware root of trust necessary for every renewable energy device?
No. It is most necessary for devices with control authority, protocol-bridging roles, sensitive credentials, or long unattended lifecycles. A practical method is to classify devices into 3 risk tiers and prioritize the highest-impact nodes first. This keeps budgets realistic while protecting the parts of the system that create the most operational exposure.
What should operators check during pilot testing?
Operators should verify secure onboarding success, update behavior, rollback logic, telemetry integrity, and network performance under realistic interference. A pilot period of 2–8 weeks is often enough to expose integration issues, especially in dense building environments or mixed-protocol networks.
Can a lower-cost supplier still meet the requirement?
Possibly, but only if the supplier can demonstrate disciplined manufacturing, secure provisioning, stable firmware processes, and credible protocol performance. This is why verified IoT manufacturers matter. The decision should rest on measurable technical evidence, not on labels like military-grade security or seamless integration.
Why consult NHI before final device selection?
Renewable energy projects increasingly depend on connected hardware that crosses protocol boundaries and operational domains. One device may sit between power, data, access, occupancy, and cloud workflows. That complexity makes superficial vendor evaluation risky. NHI helps buyers reduce uncertainty by turning claims into technical verification across connectivity, smart security, energy control, IoT hardware quality, and edge performance.
For information researchers, NHI can help clarify whether a hardware root of trust is truly required for a given architecture. For operators, the focus can shift to deployment stability, update behavior, and long-term serviceability. For procurement teams, the conversation can center on supplier comparison, sample validation, and lead-time realism. For business evaluators, the key value is a clearer link between security design and lifecycle cost.
If you are comparing smart home hardware testing results, reviewing Matter protocol data, or screening verified IoT manufacturers for renewable energy and smart building projects, NHI can support the evaluation with practical engineering logic rather than brochure language. This is especially useful when your project must balance 4 pressures at once: security, interoperability, delivery schedule, and commercial viability.
Contact NHI to discuss parameter confirmation, device role classification, protocol compatibility concerns, sample support, expected delivery windows, certification-related questions, or a tailored sourcing shortlist. If your team is deciding whether a hardware root of trust is necessary, the fastest path is to review the actual device function, network position, update model, and deployment scale before you commit to procurement.
Protocol_Architect
Dr. Thorne is a leading architect in IoT mesh protocols with 15+ years at NexusHome Intelligence. His research specializes in high-availability systems and sub-GHz propagation modeling.
Related Recommendations
- Lina Zhao (Security Analyst)Smart lock OEM China options differ most in security validation
- Lina Zhao (Security Analyst)Where smart security access control systems usually fail first
- Lina Zhao (Security Analyst)Hardware root of trust choices that affect long-term device risk
- Lina Zhao (Security Analyst)Smart Lock OEM China: How to Avoid Bad Fits
- Lina Zhao (Security Analyst)What to Ask a Smart Lock OEM Before Sampling
- Lina Zhao (Security Analyst)Smart Security Access Control: Which Setup Works Best
- Lina Zhao (Security Analyst)Hardware Root of Trust: When Is It Necessary
- Lina Zhao (Security Analyst)How to Reduce Risk When Sourcing Smart Lock Hardware
- Lina Zhao (Security Analyst)Smart Security Access Control: Which Hardware Fails First
- Lina Zhao (Security Analyst)What to Check Before Choosing a Smart Lock OEM
Analyst
